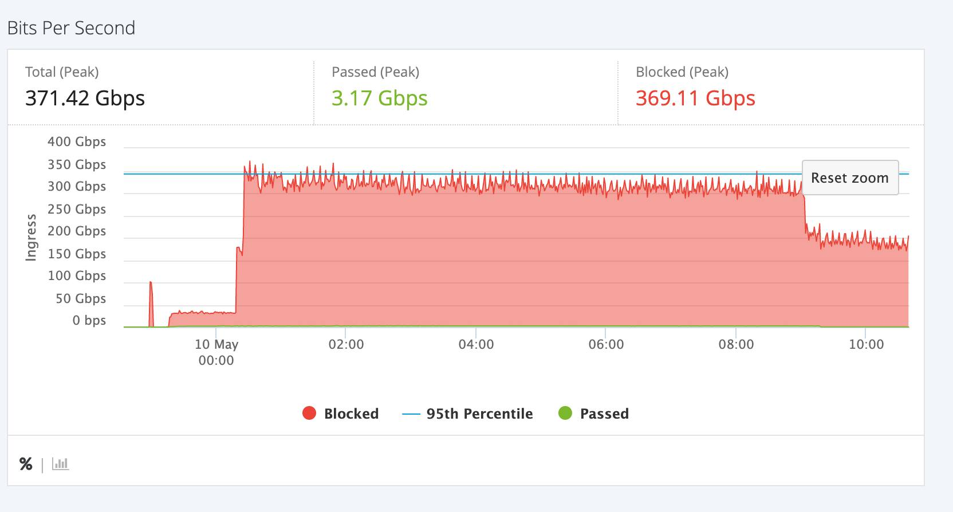
Case Studies
Large-Scale CC Attack Combined with L4 DDoS
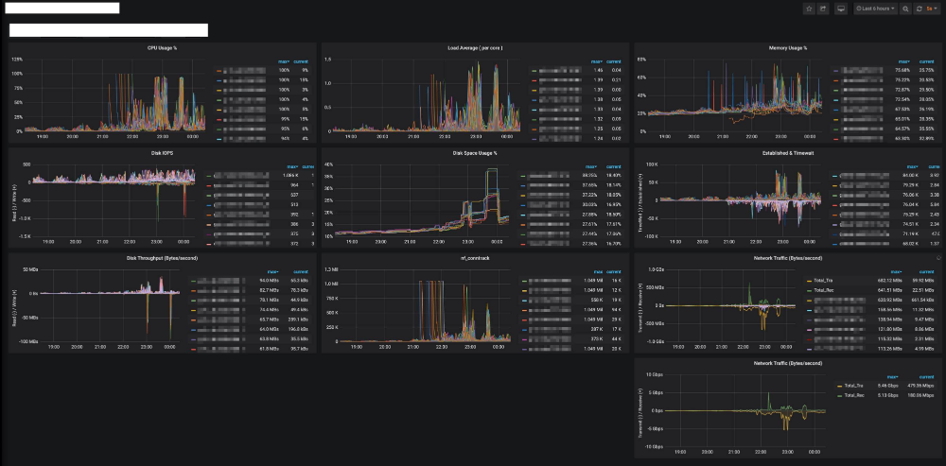
Attack Type: Primarily UDP Flood and TCP SYN Flood, aiming to exhaust network bandwidth.
Attack Scale: Total traffic peak reached 122.18 Gbps, with 121.25 Gbps of attack traffic successfully blocked, allowing only 1.28 Gbps of normal traffic through.
Defense Measures:
- Upon the attack’s onset, the Anycast architecture disperses the attack traffic across global nodes, reducing pressure on any single region.
- A small amount of HTTP Flood and application-layer CC attacks mimicking normal requests were detected and filtered by the WAF.
Defense Technology Advantages
Globally Distributed Node Network (Anycast Architecture):
Attack traffic is distributed across multiple nodes for cleaning, preventing overload on a single node.
Multi-Layer Cleaning Architecture:
From large-scale L3/L4 traffic cleaning to deep L7 application-layer cleaning, providing comprehensive protection.
Real-Time Traffic Monitoring and Dynamic Adjustment:
Cleaning strategies are updated instantly based on changes in attack patterns.
Minimized Business Impact:
Only normal traffic is allowed through, ensuring that user experience remains unaffected.
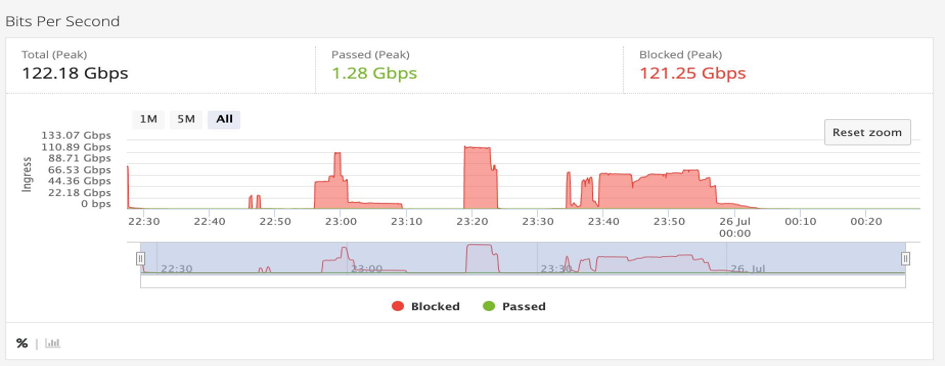
Over 1 Tbps L4 DDoS Attack
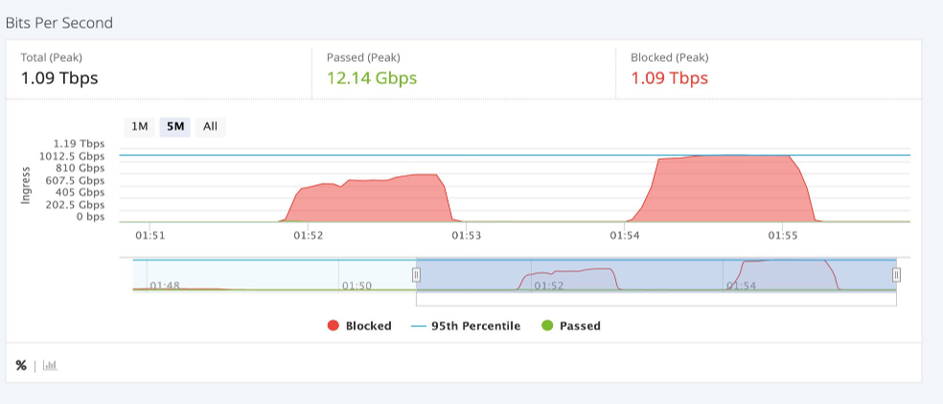
Attack Type: The attack includes UDP Flood and TCP SYN Flood (upper image), as well as DNS amplification and NTP amplification attacks (lower image).
Attack Scale:
- The upper image shows a total traffic peak of 1.09 Tbps, marking an extremely large-scale attack. Of this, 1.09 Tbps of attack traffic was successfully blocked, with only 12.14 Gbps of normal traffic passing through.
- The lower image shows a total traffic peak of 371.42 Gbps, where 369.11 Gbps of attack traffic was successfully blocked, leaving only 3.17 Gbps of normal traffic.
Defense Measures: Using Tengyun Cloud’s traffic characteristic recognition technology, abnormal traffic patterns are precisely identified, enabling further filtering of small particle attack traffic.
Defense Technology Advantages
Efficient Cleaning Capacity:
Each node supports up to 1 Tbps cleaning, capable of handling large-scale attacks.
Multi-Layer Defense Strategy:
Protection across all layers from L3/L4 to L7, offering comprehensive defense.
Intelligent DNS Scheduling:
Ensures that attack traffic is cleaned close to its source, minimizing latency.
Application Layer Cleaning:
A powerful WAF effectively handles HTTP Flood and CC attacks, demonstrating the company’s technical advantages in application layer protection.
Intermittent Large-Scale Traffic and Packet Flood
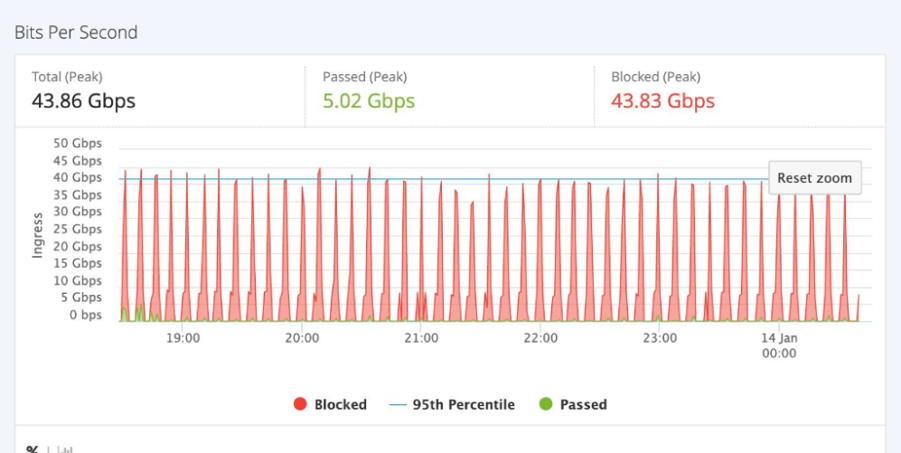
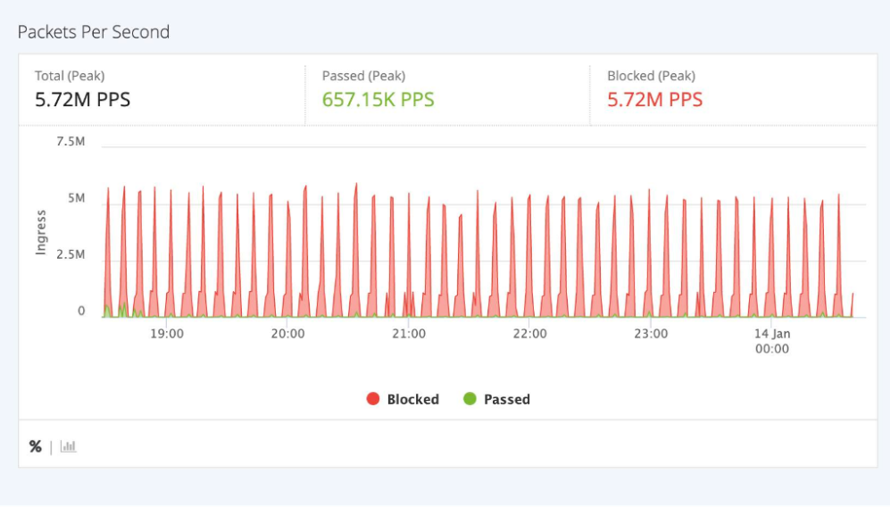
Attack Type: Periodic peak attacks manifest as intermittent large-scale traffic and packet floods.
Attack Scale:
- Total traffic peak: 43.86 Gbps
- Peak packet rate: 5.72 million packets per second (M PPS)
- Blocked Traffic: 43.83 Gbps and 5.72 M PPS of malicious traffic were successfully intercepted.
- Normal Business Traffic: 5.02 Gbps and 657.15 K PPS of normal traffic passed through unaffected.
Defense Measures: Malicious traffic and high packet rate attacks were intercepted at the L3/L4 layer, with secondary cleaning identifying and blocking residual traffic.
Defense Technology Advantages
Efficient Cleaning Capability:
In the primary cleaning stage, most attack traffic (43.83 Gbps and 5.72 M PPS) was intercepted.
Multi-Layer Cleaning Architecture:
A complete defense loop is formed through L3/L4 layer high-volume interception and L7 layer deep application protection.
Intelligent Scheduling Technology:
Quick diversion and efficient interception of attack traffic minimize the impact on normal business traffic.
Application Layer Protection:
A powerful WAF provides deep detection and interception capabilities, delivering precise application layer protection.
20 Million Connection Request CC Attack

Attack Scale:
- Maximum connection peak: Nearly 20 million connection requests
- Attack Mode: Application-layer CC attack simulating legitimate user connection behavior, aimed at exhausting the server’s application resources and causing service downtime.
Defense Measures:
- Web Application Firewall (WAF): Detects and intercepts abnormal high-frequency requests, such as a large number of repetitive requests within a short time frame.
- Deep HTTP Request Behavior Analysis: Filters out malicious connections simulating legitimate user actions.
- Behavior Analysis & Limitation: Dynamically limits connection count and request frequency from a single source IP, quickly identifying and isolating the attack source.
Defense Technology Advantages
Application Layer Deep Protection:
WAF focuses on defending against L7 layer attacks, effectively handling CC attacks and HTTP Floods, which are complex threats.
Network Feature Analysis:
Real-time monitoring and dynamic adjustment of limitation rules enable quick adaptation to attack patterns.
Multi-Layer Cleaning Collaboration:
Works in coordination with L3/L4 layer primary interception and L7 layer deep cleaning, forming a comprehensive defense system.

